Overview – Network & Port Forwarding
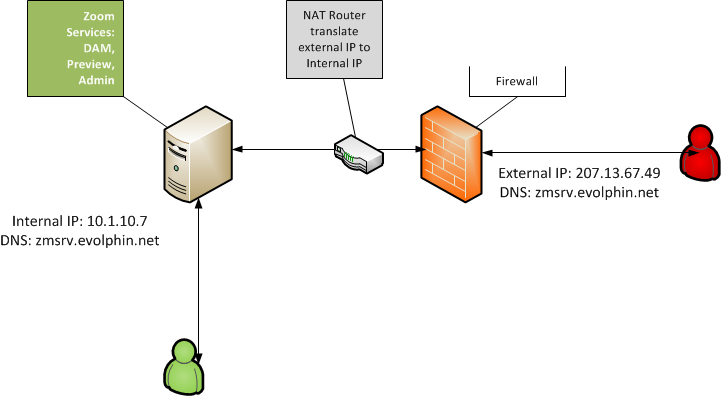
You need to provide external users such as partners, clients or remote employees the ability to connect to Zoom services from outside the firewall or intranet. You also need ensure internal users continue to connect to Zoom from within the firewall without looping out and coming back through an external IP address. You might also wish to have Zoom services access via standard 443 (HTTP SSL/TLS), 80 (HTTP) ports to avoid users hitting firewall blocking of non-standard ports. Visually, you want to setup access as below:
Prerequisites
- DNS and Network Admin who knows how to manage external and internal DNS:IP mapping
- Internal DNS resolver for Zoom hostnames to resolve to internal IPs
- External DNS resolver for Zoom hostnames to resolve to external IPs
- Knowledge of firewalls
- SSL/TLS certificate knowledge
Solution for External to Internal NAT
Setup DNS entries such that in the internal network, the host name resolves to internal IP address and to the external IP address outside the firewall. For example in the above diagram, zmsrv.evolphin.net resolves to IP 10.1.10.7 and externally to IP 207.13.67.49.
Note: This typically requires two DNS servers or in the DNS server conditional rules to resolve hostnames to different internal or external IP based on user’s context
This needs to be done for whichever Zoom service needs to be exposed from outside the firewall. For example, for just web client access, you need to do this for only Zoom Preview Server and not Zoom DAM/MAM server.
Now configure the Zoom settings in the Web Management Console for the specific server as described below. Assuming you want both Zoom & Preview server exposed through the firewalls:
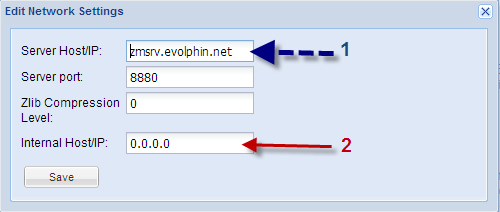
- Go to Server Control Panel. Click on Network Settings to change Zoom server Host name/IP address to point to the DNS host name for e.g. zmsrv.evolphin.net
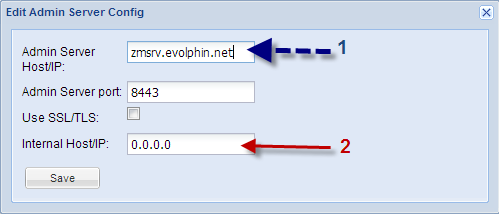
- In the Server Control Panel click on Admin Server config to change Admin Server Host/IP to point to the DNS host name for e.g. zmsrv.evolphin.net
- 5.1 or higher: Edit the server.xml and preview-server.xml for Preview server settings to point to the DNS host name.
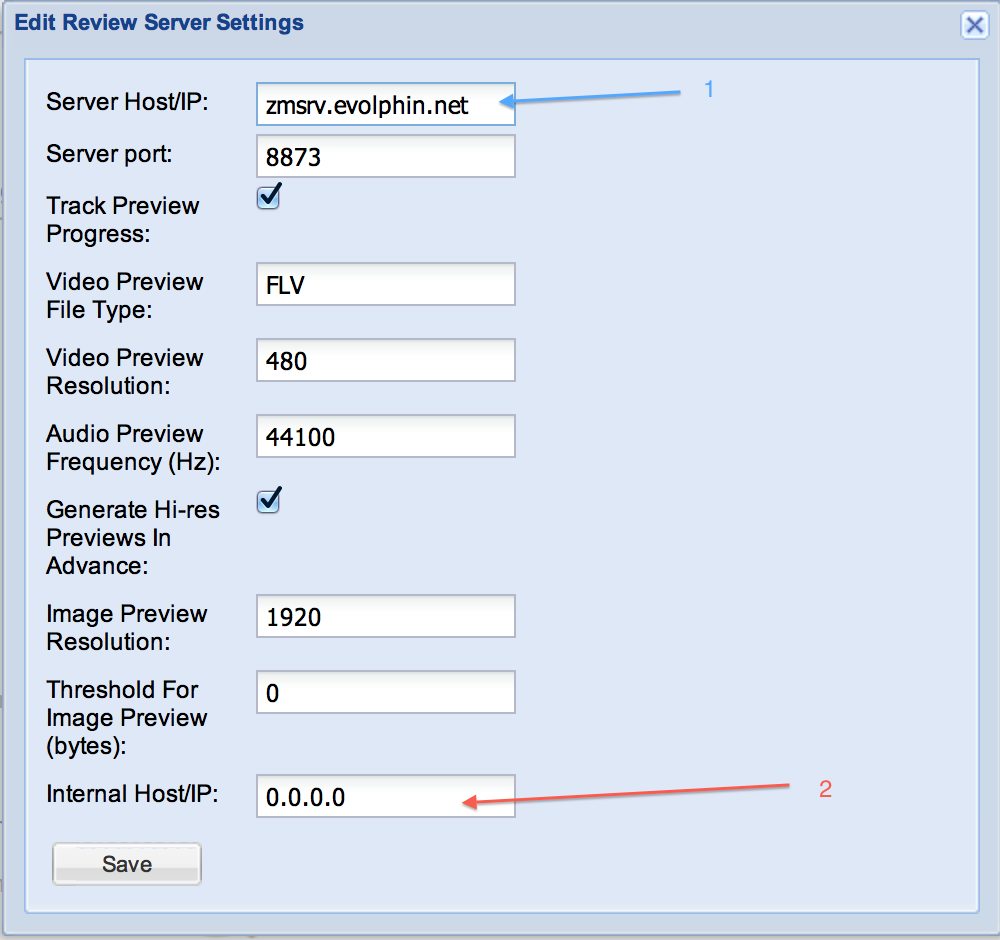
- 5.0 or below: In the Server Control Panel click on Preview Server Settings to change Server Host/IP to point to the DNS host name for e.g. zmsrv.evolphin.net. If the preview server is on a different IP or host name, set the appropriate DNS host name.
- Forward Zoom ports from external IP to internal. Default TCP ports are listed here.
- Restart the Zoom Asset Browser on the client desktop and use the DNS host name (for e.g. zmsrv.evolphin.net from above scenario) to connect to the Zoom server
- If only Web Client access is desired from outside the firewall, forward only the 8973 (Preview HTTPS) port.
Note: It is strongly recommended to first setup SSL/TLS certificates for any hosts exposed outside the firewall. Do not forward insecure (HTTP) ports such as 8873 or 8443. These days you can easily generate and convert Lets Encrypt free SSL certificates (PEM format) for use in Java based keystore (PKCS12 format). If using Let’s Encrypt don’t forget to setup automatic renewal. Your network security admin should know how to manage SSL/TLS and/or Let’s Encrypt certificates for your organization.
Solution for Port Forwarding
You can use the solutions described below to forward any Zoom port including 8880, 8443, 9880, 8973, 8443, 9443.
Windows Server
You can change the default ports via the Web Management Console as described in the previous sections. For e.g. you could change the Preview Server port to listen on port 443 instead of 8873 or 8973 (SSL). Windows does not have restriction on privileged ports (< 1024) like UNIX, so simply changing the ports can work.
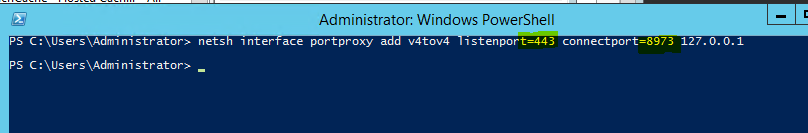
Other option would be to setup port forwarding on the Windows Server using the netsh CLI. For example the rule below will forward traffic on HTTPS port 443 to the Zoom Preview Server SSL port.
Linux Server
On UNIX system any port < 1024 is treated as a privileged port and a non-root process can’t bind to it. Zoom services like DAM/MAM server, Preview server by default are run as non-root user such as ‘evolphin’. In order for such services to listen on privileged ports, port forwarding can be setup in the Linux kernel. The steps below assume firewalld (wrapper on top of iptables) has been installed:
- Check the active zones
[root@srdam-zoom ~]# firewall-cmd --get-active-zonestrustedinterfaces: eth0 - Add the port forward rule to the appropriate Zone (public/external/trusted etc). Please see the documentation for the firewall if needed.
[root@srdam-zoom ~]# firewall-cmd --permanent --zone=trusted --add-forward-port=port=443:proto=tcp:toport=8973
[root@srdam-zoom ~]# firewall-cmd --reload - Confirm if the port was forwarded
[root@srdam-zoom ~]# firewall-cmd --list-forward-ports
port=443:proto=tcp:toport=8973:toaddr= - Try accessing the service now over the standard secure port via an HTTPS URL. For e.g.
https://mypreviewserver.mydoamin.com/webclient