For many organizations, LDAP Server is a key way to allow their users to log into multiple systems. Evolphin Zoom has native support to integrate with your LDAP Server, including popular Directory Services, like Microsoft Active Directory and Novell Directory Service. The following instructions provide you with information on how to fetch the desired subset of existing users, groups, and other associations from your LDAP Server into Zoom.
Make sure that Directory Service is installed and configured on your LDAP Server. If using, then SSL is also enabled and configured on your LDAP Server. Admin access to your LDAP Server should be available.
Prepping your LDAP Server
Before moving user information to Zoom, you need to identify what should be copied to Zoom. Identify:
- Users that should be copied to Zoom.
- If any roles should be created in Zoom. Also, which of these roles should be mapped to some, all, or none of these users.
- If any projects (existing in Zoom) should be assigned to some or all of these users.
Firstly, locate the users for pulling into Zoom. All of these users should belong to one common group that will be called the Zoom Filter group. Any user with an email, that also belongs to this Zoom Filter group, will be copied to Zoom.
Additionally, you can also identify other groups that will map as roles in Zoom. These other groups should also be a member of the Zoom Filter group. Each user that should automatically get one or more of these roles in Zoom should be mapped correspondingly to one or more of these other groups on the LDAP Server as well. Roles may also have no users mapped to them.
Lastly, you can also check which Projects in Zoom you would want to automatically assign to one or more of these users. Each user that should automatically be assigned one or more projects in Zoom should have the same project names set in their Project attribute on the LDAP Server as well.
On your LDAP Server, make sure to:
- Configure one group as the Zoom Filter Group containing all users that you wish to copy to Zoom.
- These users’ mail attributes should be filled in.
- Optionally, configure additional groups that are also members of the Zoom Filter Group.
- Additionally, each of these users may also be assigned to zero or more of these groups.
- Optionally, these users also have their Project attribute filled in. The project name is case-sensitive and the project should also already exist in Zoom.
Zoom Filter Group
In order to pull users & groups from the LDAP Server into Zoom, a filter group must be created in the LDAP Server’s database first. For example, CN=ZOOM_DAM_USERS, OU=Enterprise Apps, DC=corp,DC=acme,DC=com in the diagram below:
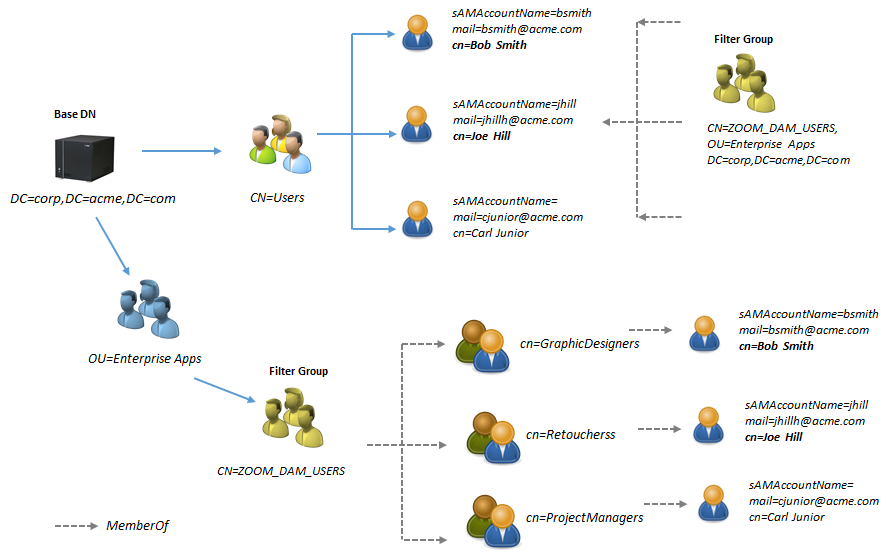
In addition, it is recommended to create Security Groups in the LDAP Server for the permissions that Zoom support, these permissions must be applied to the groups after these have been pulled into Zoom:
| Permission | Effect |
| None | Has no access to any resource |
| Distribute | Can read only published project items |
| Review | Inherits Distribute permission and can read those project items that have been marked for review |
| Read | Inherits Review permission and can read/view any resource |
| Contribute | Inherits Read permission and can add new items |
| Edit | Inherits Contribute Permission and can delete their own items |
| Edit_All | Inherits Edit Permission and can delete all items |
| Administer | Inherits Edit_All Permission and can change project configuration |
Any user or group in the LDAP Server must be a member of the Zoom filter group in order to be pulled into Zoom. That implies that you need to add users to both the Zoom filter group as well as the groups you will be pulling. If you failed to add users to the groups you wish to pull, the groups will be empty in Zoom after import.
Also, the “mail” attribute needs to be set for each user you wish to pull into Zoom. If the “mail” attribute is missing the user will not be pulled into Zoom.
What will be read from the LDAP Server?
At the minimum, all users that have emails configured and are assigned to the Zoom Filter group will be read and pulled into Zoom. Additionally:
- If these users also belong to other groups that are members of the Zoom Filter group, then these groups will be created as Roles and automatically mapped to these users in Zoom. The roles will be created under the masterldap role that already exists in Zoom.
- From Zoom 7.5 onwards, if these users also have a Project attribute assigned on the LDAP Server and these projects already exist in Zoom (case-sensitive), then these Projects are also automatically assigned to these users in Zoom. If the Project attribute has a Project name that does not exist in Zoom, then it is skipped.
| On the LDAP Server | First-time pull in Zoom | Subsequent pull in Zoom |
| Users belong to the Zoom Filter group. | Users are created and mapped to masterldap role.
Zoom admins will need to update roles and assign projects for these users. | Users are added or removed from Zoom as per their membership in the Zoom Filter group on the LDAP Server. |
| Users belong to the Zoom Filter group.
Other groups are also members of the Zoom Filter group. Some users belonging to the Zoom Filter group also belong to some of these other groups. | Users are created. Roles are created under the masterldap role from the groups on the LDAP Server. (Only groups that are members of the Zoom Filter group)
Users assigned to their corresponding role as per the group they belonged to. If a user only belonged to the Zoom Filter group, she will be assigned the masterldap role. If the other group has no users, then the corresponding role in Zoom will have no user assigned to it. These newly-created roles will have permission set to None and will be assigned all projects. Zoom admins will still need to assign projects for these users. | Users are added or removed from Zoom as per their membership in the Zoom Filter group on the LDAP Server.
Roles are added or removed from Zoom as per the membership of groups in the Zoom Filter group on the LDAP Server. |
| Users belong to the Zoom Filter group.
Some users have Projects assigned to them (with names that also exist in Zoom) | Users are created, mapped to masterldap role, and projects assigned as read from the LDAP Server. (Project names are case-sensitive and should exist on Zoom)
Zoom admins will need to update roles for these users and assign projects for users that didn’t have Project attribute set on the LDAP Server. | Users are added or removed from Zoom as per their membership in the Zoom Filter group on the LDAP Server.
New projects are associated with users when added on the LDAP Server. But, projects are never unassigned from the Zoom user when removed from the user on the LDAP Server. |
| Users belong to the Zoom Filter group.
Some users have Projects assigned to them (with names that also exist in Zoom) Other groups are also members of the Zoom Filter group. Some users belonging to the Zoom Filter group also belong to some of these other groups. | Users are created and projects assigned as read from LDAP Server. (Project names are case-sensitive). Roles are created under the masterldap role from the groups on the LDAP Server. (Only groups that are members of the Zoom Filter group)
Users assigned to their corresponding role as per the group they belonged to. If a user only belonged to the Zoom Filter group, it will be assigned the masterldap role. If the other group has no users, then the corresponding role in Zoom will have no user assigned to it. These newly-created roles will have permission set to None and will be assigned all projects. Zoom admins will still need to assign projects for users that didn’t have Project attribute set on the LDAP Server. | Users are added or removed from Zoom as per their membership in the Zoom Filter group on the LDAP Server.
Roles are added or removed from Zoom as per the membership of groups in the Zoom Filter group on the LDAP Server. New projects are associated with users when added on the LDAP Server. But, projects are never unassigned from the Zoom user when removed from the user on the LDAP Server. |
Setting up LDAP without SSL
To configure LDAP in Zoom, you need to:
- Save LDAP settings
- Update to LDAP Realm
- Pull users from LDAP Server
Follow the sections below to see the steps:
Saving LDAP Settings
- In your preferred web browser, open the Web Management Console.
- Log in using your Zoom admin credentials.
- In the left sidebar, click Server Control Panel under the Server section.
- Click LDAP Server Settings.
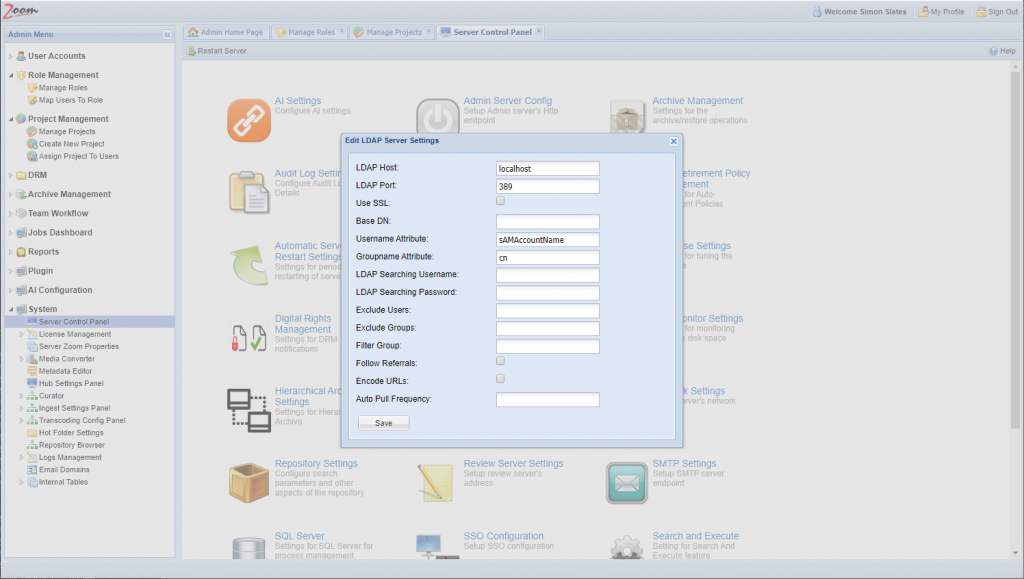
- Fill in the following values to meet your organization’s needs:
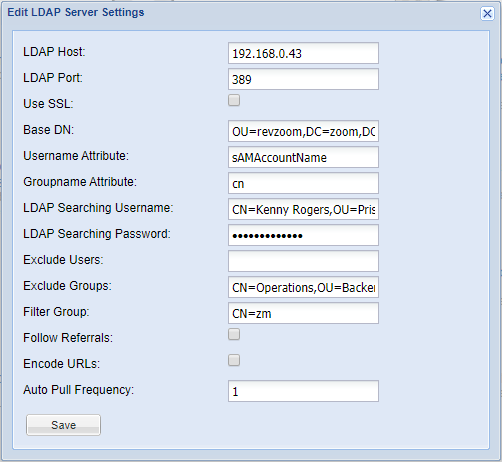
Field Description Host The machine IP/Hostname where LDAP Server is running Port Port number where the LDAP Server is listening. Default 389 Use SSL See section “Setting Up LDAP (with SSL)“ Base DN The distinguished name of the base context in the LDAP repository within which the users and groups defined; this will act as the base container from which any lookup/search will execute. If you have thousands of users in LDAP, please create an appropriate container to limit the search scope. Note: If you have multiple OU organizational units that you are referring to for your users, your base DN needs to encapsulate both OUs.Ex. CN=Users,DC=ZOOM,DC=local Username Attribute The attribute that would mark the username.Ex. sAMAccountName Groupname Attribute The name of the attribute that would mark the name of the group: typically, cn for any group entry. Ex. CN LDAP Searching Username The DN of the user name entity that will be used to bind to the LDAP Server. This username must be a member of a group with enough privileges to be able to search the LDAP db.Ex. ZOOM\Administrator or CN=Administrator,CN=Users,DC=ZOOM,DC=local LDAP Searching Password The password associated with the searching username. Exclude Users A comma-separated list of user DNs to ignore Exclude Groups A comma-separated list of group DNs to ignore Filter Group The DN of a group that will contain all users who would operate with Zoom, and also all the groups that the users are organized into.Ex. CN=ZOOM_DAM_USERS, OU=Enterprise Apps, DC=corp,DC=acme,DC=com in the diagram above. Follow Referrals* Enable this when using multiple LDAP Servers. Encode URLs* Enable this if spaces or special characters are used in the user names, organizational units, or groups. Auto Pull Frequency† Specify the number (in days) for the frequency at which information will be pulled again from the LDAP Server. This will get information about any change in users/projects/roles. * Available from Zoom 7.5 onwards.† Available from Zoom 7.3 onwards. - Click Save. Settings should look similar to sample settings below:
- You will be prompted to restart the server. Click Yes.
LDAP Settings are saved in Zoom.
Updating to LDAP Realm
- In your preferred web browser, open the Web Management Console.
- Log in using your Zoom admin credentials.
- In the left sidebar, click Server Control Panel, then click Security Settings and verify the security realm is switched to ExtLdapRealm, if not change it to :
ExtLdapRealm. This will switch the authentication provider to LDAP from the local Zoom user database.This is an irreversible switch, please make sure you really want to do this before switching.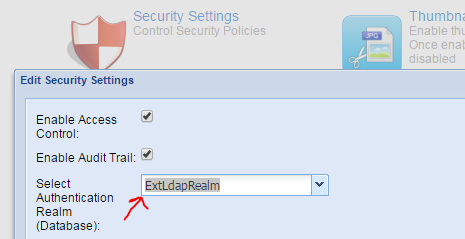
The Realm is now updated.
Pulling users from your LDAP Server
- In your preferred web browser, open the Web Management Console.
- Log in using your Zoom admin credentials.
- In the left sidebar, click Manage accounts under User Accounts.
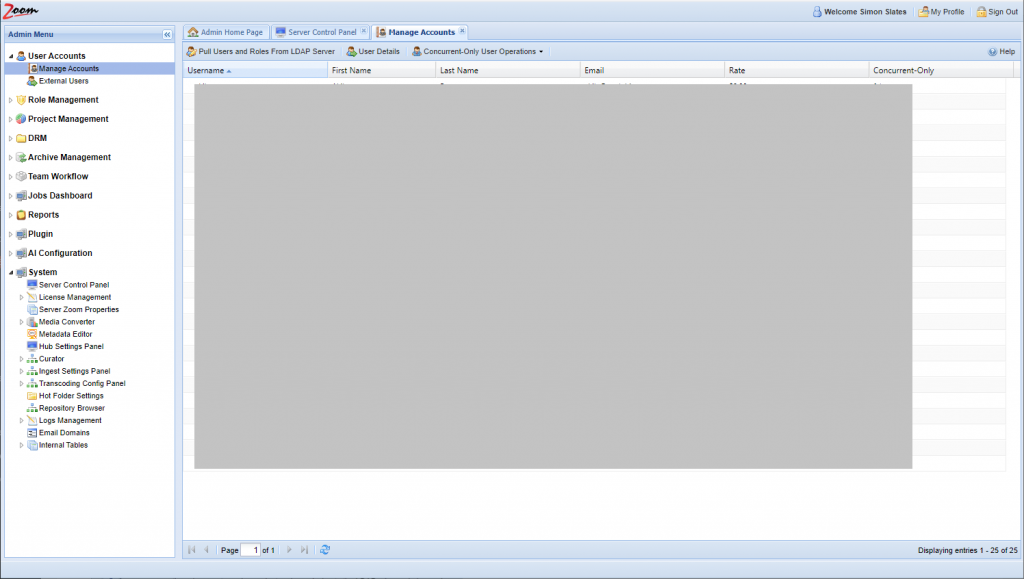
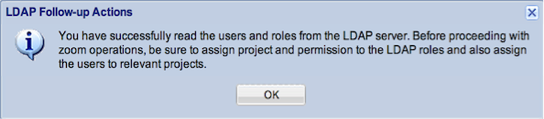
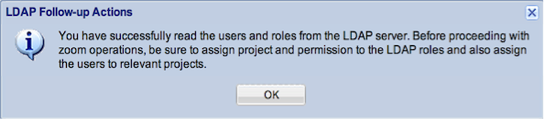
- Click Pull Users and Roles From LDAP Server.If successful, you should see a list of the names in your Security Group listed in the manage accounts and the following dialog:
Setting Up LDAP with SSL
The following sections describe how to configure the specific items to allow LDAP to authenticate over SSL using Microsoft Active Directory. These instructions assume that the base configurations were applied in section, Setting Up LDAP without SSL.
Exporting Certificate from Active Directory
Windows 2012
- Log into your Active Directory server using Administrator credentials.
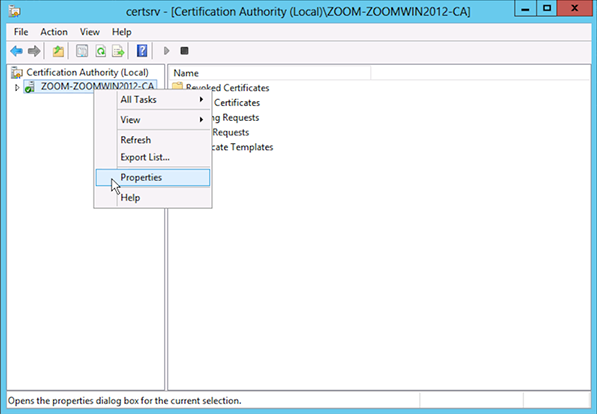
- Search for certsrv.msc

- Click Enter on your keyboard.
- Select Certification Authority in the left sidebar, right-click and select Properties.
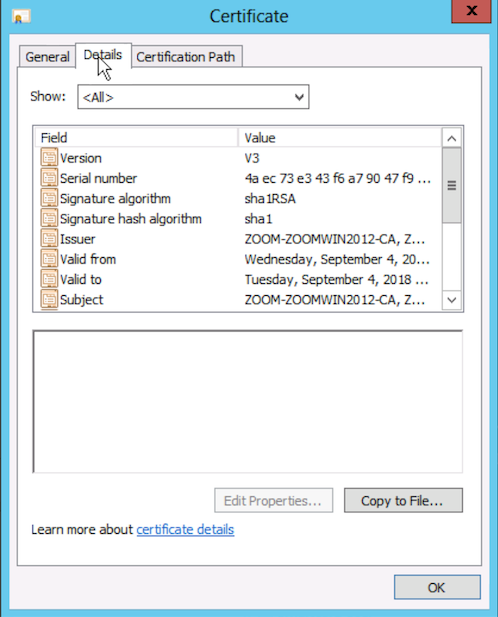
- Select the Details tab.
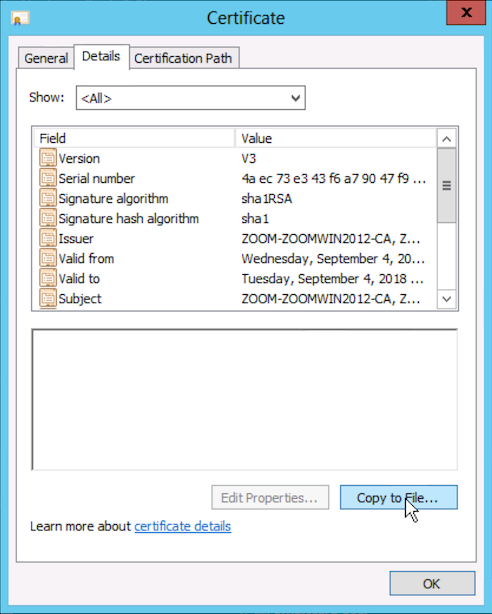
- Click the Copy to file… button.
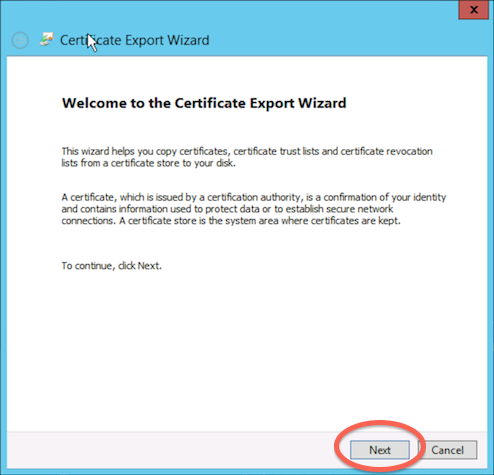
- Click Next.
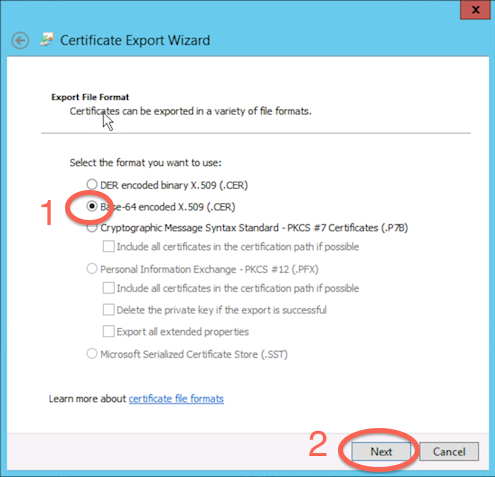
- Select Base-64 encoded X.509 (.CER) and click Next.
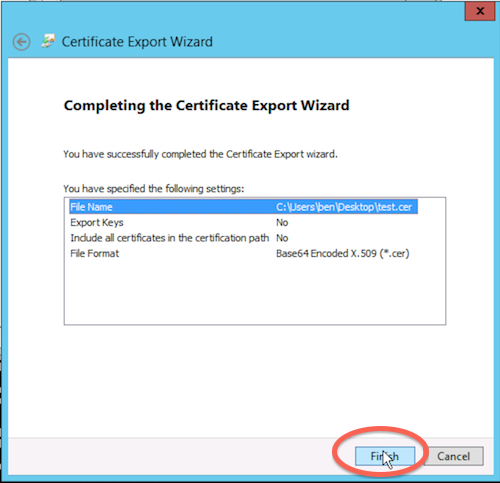
- Click Browse… and select your desired location to export the certificate file to. Then click Next.
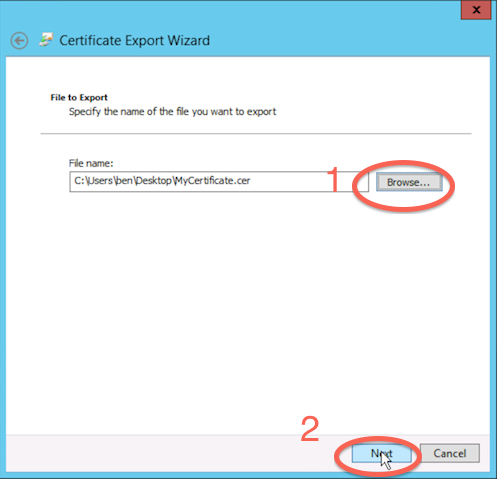
- Click Finish.
Importing Certificate from Active Directory
In order for Zoom to properly connect to Active Directory using SSL, it will need to import the certificate into its Keystore. The following instructions describe how to import the Active Directory certificate into the Java JRE.
NOTE: You need the Java keytool.exe installed on the machine. If it is not installed with your Evolphin JRE, install a different JRE on your computer. You may need to set your absolute path in order to run the keytool.exe command.
- Click Start menu.
- Search for cmd.
- Right-click on Command Prompt.
- Select Run as Administrator.
- Type into Command Prompt:
cd "C:\Program Files (x86)\Evolphin\DAM\jre\lib\security"
- Hit Enter.
- Type into the Command Prompt:
keytool -import -alias adcert -file <INSERT PATH TO CERTIFICATE> -keystore cacertsMake sure that your path is in quotation marks to escape the spaces in the path.The cacerts is relative to where you are in the command line, so if you are not in the security folder, you can put an absolute path here.
The keytool application is not packaged along with the Zoom server. You can find it in any regular JRE installation. - You will be prompted to enter the keystore password. By default, the password is changeit.
- Hit Enter.
- You will be prompted whether you want to trust this certificate. Hit Yes.
- Hit Enter.
Your certificate should now have been installed correctly.
Move to the next section to enable SSL for LDAP connections in Zoom.
Configuring SSL for LDAP in Zoom
These instructions have been truncated for SSL specific settings. For other settings, please refer to Setting Up LDAP without SSL
- In your preferred web browser, open the Web Management Console. ex. http://localhost:8443 or http://<zoomserver>:8443
- Log in using your admin credentials.
- In the left sidebar, click Server Control Panel under the Server section.
- Click LDAP Server Settings.
- Under LDAP Port, type 636. 636 is the default SSL port for LDAP
- Check the box Use SSL.
- Click Save.
- You will be prompted to restart the server. Click Yes.
- Refresh your web browser.
- Log in using your admin credentials.
- In the left sidebar, click Manage accounts under User Accounts.
- Click Pull Users and Roles From LDAP Server.If successful, you should see a list of the names in your Security Group listed in the manage accounts and the following dialog: